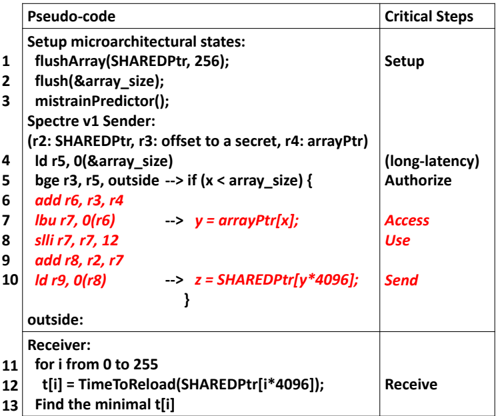
## Table: Pseudo-code Execution with Critical Steps
### Overview
The image presents a structured table mapping pseudo-code execution steps (left column) to critical security-related operations (right column). The pseudo-code appears to implement a Spectre v1 attack, with specific instructions highlighted in red. Critical steps are categorized into Setup, (long-latency) Authorize, Access Use, Send, and Receive phases.
### Components/Axes
- **Left Column (Pseudo-code)**:
- Line numbers 1–13 with assembly-like instructions and Spectre attack logic.
- Key operations: `flushArray`, `flush`, `mistrainPredictor`, `ld` (load), `bge` (branch if greater than or equal), `lbu` (load byte unsigned), `slli` (shift left logical immediate), `add`, and `id` (load double).
- Red-highlighted instructions: `add r6, r3, r4`, `lbu r7, 0(r6)`, `slli r7, r7, 12`, `add r8, r2, r7`, `ld r9, 0(r8)`, and `z = SHAREDPtr[y*4096]`.
- **Right Column (Critical Steps)**:
- **Setup**: Initialization of microarchitectural states (`flushArray`, `flush`, `mistrainPredictor`).
- **(long-latency) Authorize**: Branch and load operations (`bge`, `ld`) to validate memory access.
- **Access Use**: Memory access via `lbu` and pointer dereference (`y = arrayPtr[x]`).
- **Send**: Shared pointer dereference (`z = SHAREDPtr[y*4096]`).
- **Receive**: Time measurement loop (`TimeToReload`) to infer secret values.
### Detailed Analysis
1. **Setup Phase**:
- `flushArray(SHAREDPtr, 256)` and `flush(&array_size)` clear cache lines to establish a baseline.
- `mistrainPredictor()` resets branch prediction state.
2. **Sender Logic**:
- Variables `r2` (SHAREDPtr), `r3` (offset), `r4` (arrayPtr), and `r5` (array_size) are initialized.
- A loop (`bge r3, r5, outside`) iterates over `array_size`, with red-highlighted instructions modifying registers to compute memory addresses.
3. **Critical Memory Access**:
- `lbu r7, 0(r6)` accesses `arrayPtr[x]` (highlighted in red), triggering a cache timing side channel.
- `slli r7, r7, 12` and `add r8, r2, r7` compute the offset for the shared pointer dereference.
4. **Secret Inference**:
- `ld r9, 0(r8)` loads the value at the computed address, and `z = SHAREDPtr[y*4096]` captures the result.
- The `Receive` phase measures reload times (`TimeToReload`) to deduce the secret value via Spectre's cache-based timing attack.
### Key Observations
- **Red-highlighted instructions** (`add`, `lbu`, `slli`, `add`, `ld`, `z = SHAREDPtr`) represent the core Spectre attack logic, manipulating registers to leak memory contents.
- The `(long-latency) Authorize` step introduces a delay, likely to bypass branch prediction defenses.
- The `Receive` phase (lines 11–13) iterates 256 times to sample reload times, identifying the minimal `t[i]` to infer the secret.
### Interpretation
This pseudo-code demonstrates a Spectre v1 attack, exploiting speculative execution to bypass memory safety. The **Setup** phase prepares the environment, while **Authorize** and **Access Use** steps manipulate branch prediction and memory access. The **Send** and **Receive** phases exploit cache timing to infer secret values. The red-highlighted instructions are critical for bypassing security mechanisms, showcasing how speculative execution can be weaponized for side-channel attacks. The structured mapping of code to critical steps emphasizes the attack's phases, from initialization to secret extraction.