## Diagram: Secure Computation Model
### Overview
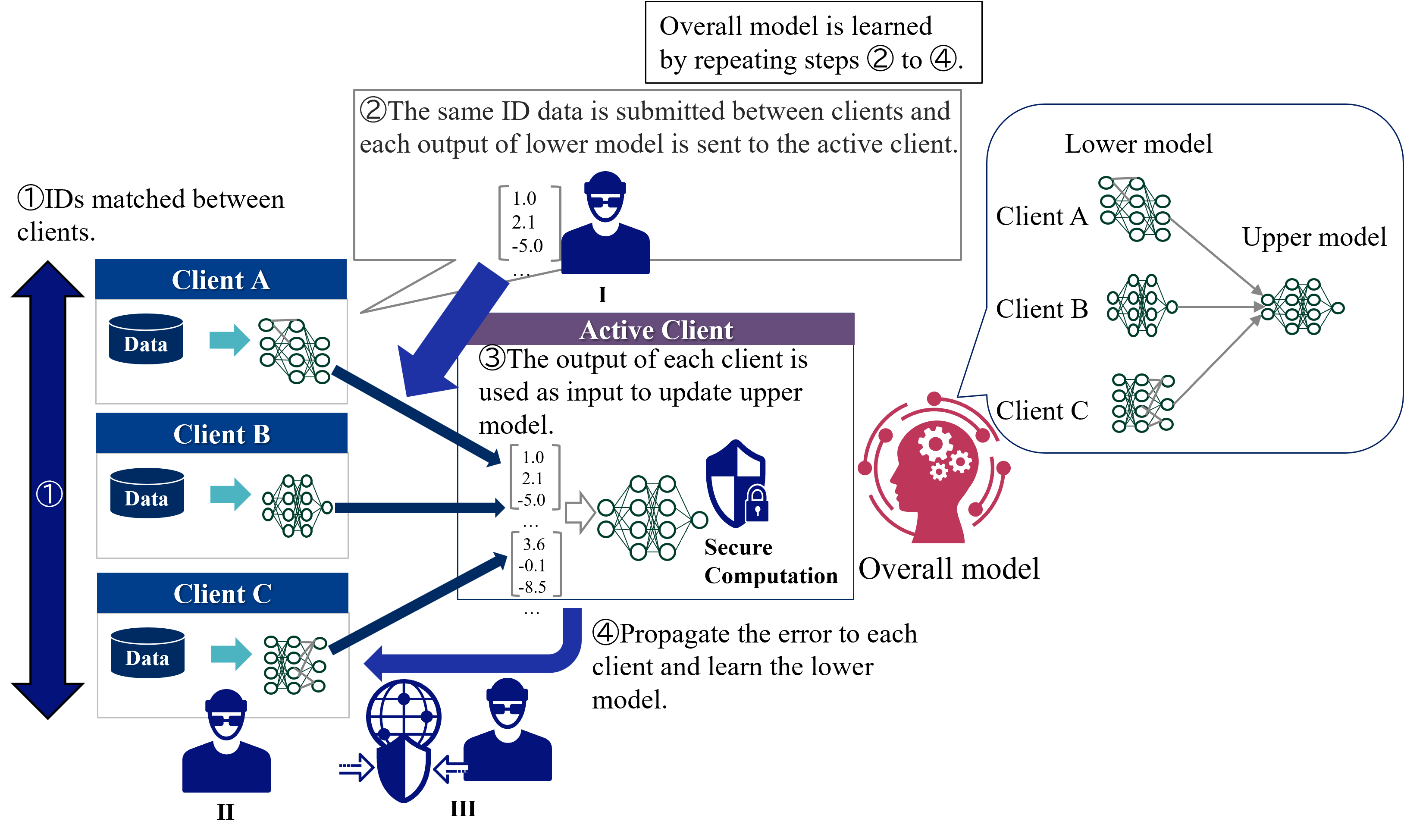
The image illustrates a secure computation model involving multiple clients (A, B, and C), an active client, and an overall model. The diagram outlines the flow of data and computations between these components, emphasizing the iterative process of learning the overall model while maintaining data privacy.
### Components/Axes
* **Clients (A, B, C):** Represented as rectangular boxes with the client name and a "Data" storage icon. Each client also has a neural network representation.
* **Active Client:** A central processing unit that receives data from the clients and updates the upper model.
* **Overall Model:** A representation of the final learned model, depicted as a head with gears inside, symbolizing computation.
* **Lower Model:** Neural networks associated with each client.
* **Upper Model:** A neural network that combines the outputs of the lower models.
* **Secure Computation:** A shield icon with a lock, indicating the use of secure computation techniques.
* **Arrows:** Indicate the flow of data and computations.
* **Numerical Data:** Vectors of numbers representing data being passed between clients.
* **Numbered Steps:** Indicate the sequence of operations in the model.
### Detailed Analysis
The diagram outlines a four-step process:
1. **IDs matched between clients:** A large blue arrow pointing downwards indicates the matching of IDs between clients A, B, and C.
2. **The same ID data is submitted between clients and each output of lower model is sent to the active client:** Data from each client is sent to the "Active Client" (labeled as 'I'). The data is represented as vectors of numbers:
* Client A: \[1.0, 2.1, -5.0, ... ]
* Client C: \[3.6, -0.1, -8.5, ... ]
A man icon is present near the active client.
3. **The output of each client is used as input to update upper model:** The active client processes the data and updates the upper model. A secure computation icon (shield with a lock) is shown.
4. **Propagate the error to each client and learn the lower model:** The error is propagated back to each client, and the lower models are updated. This is represented by a blue arrow pointing from the "Overall Model" back to the clients. A globe icon with a shield is present.
The diagram also shows a "Lower model" and "Upper model" section on the right side. The lower model consists of neural networks for each client (A, B, and C). The outputs of these lower models are combined in the upper model.
Two additional man icons are present, labeled II and III.
The text "Overall model is learned by repeating steps 2 to 4." is present at the top of the diagram.
### Key Observations
* The diagram illustrates a federated learning approach where clients contribute to a global model without sharing their raw data directly.
* Secure computation techniques are used to protect data privacy during the learning process.
* The model involves iterative updates of both lower and upper models.
### Interpretation
The diagram presents a secure federated learning framework. The clients (A, B, and C) each possess local data. The process begins with matching IDs across clients. The data is then processed locally by each client's "lower model." The outputs of these lower models are sent to an "active client," which aggregates the information and updates an "upper model." Secure computation techniques are employed to ensure data privacy during this aggregation. The error from the upper model is then propagated back to the clients, allowing them to refine their lower models. This iterative process (steps 2-4) continues until the overall model converges. The presence of man icons near the data flow suggests potential security considerations or roles within the system. The globe icon with a shield further emphasizes the security aspect of the data transfer.