TECHNICAL ASSET FINGERPRINT
a61942c39287576cf5b7f2af
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
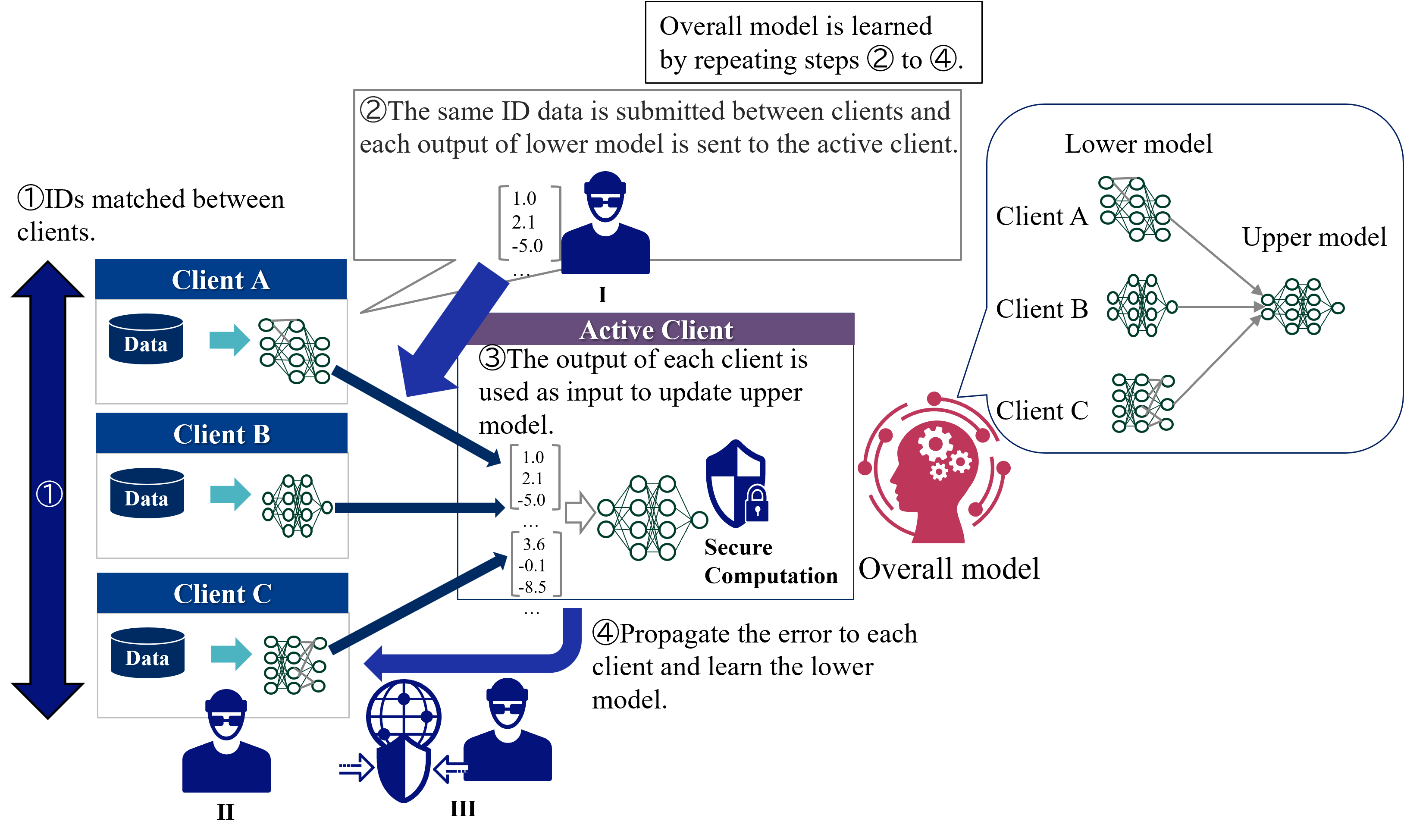
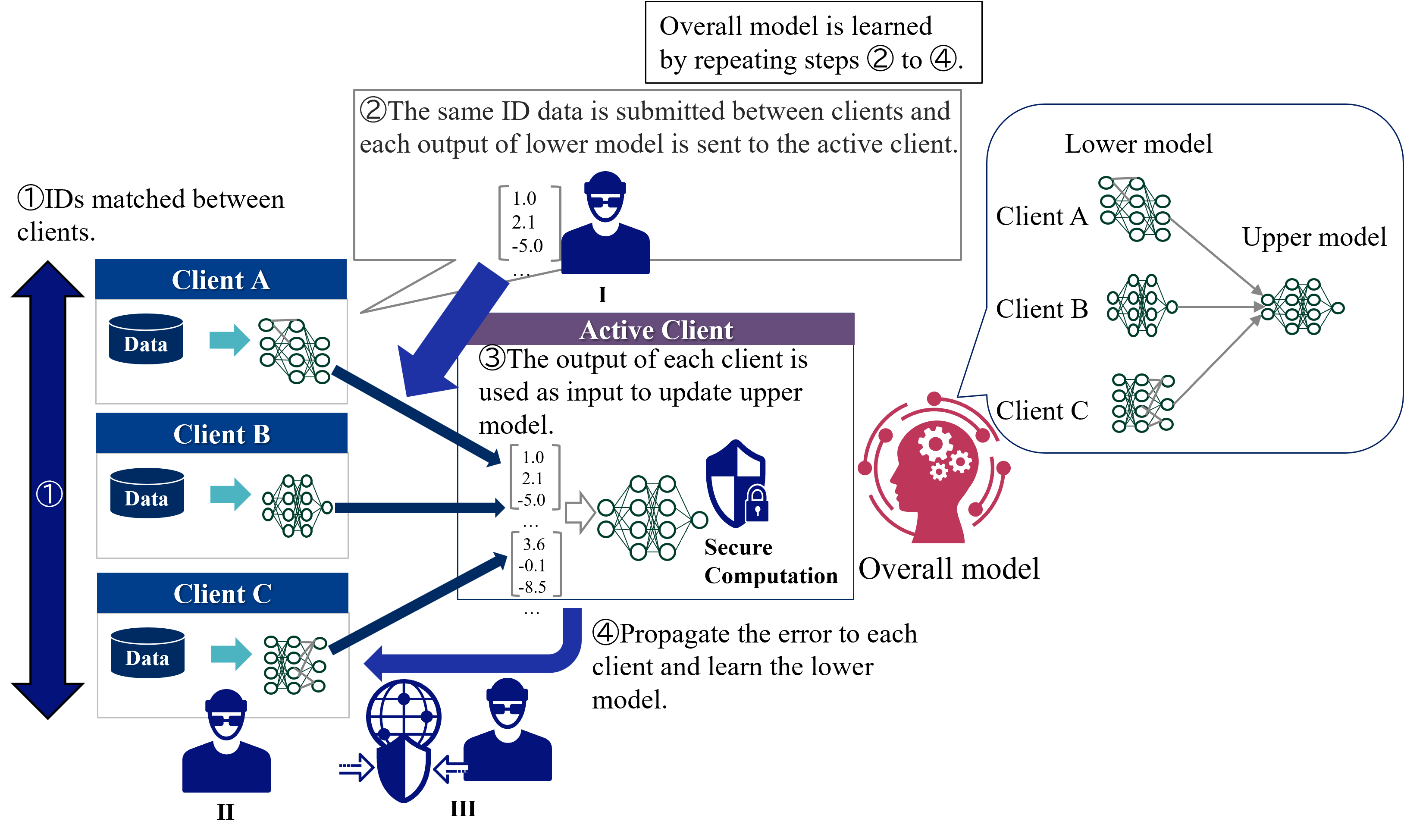
## Technical Diagram: Federated Learning with Secure Computation
### Overview
The image is a technical diagram illustrating a multi-step, iterative process for training a federated machine learning model across multiple clients (Client A, Client B, Client C). The process involves matching client IDs, exchanging model outputs, updating a central "Upper model" via an "Active Client," and propagating errors back to update client-specific "Lower models." A key component is "Secure Computation," represented by a shield icon, indicating privacy-preserving operations. The overall model is learned by repeating steps ② to ④.
### Components/Elements
The diagram is segmented into several key regions and components:
**1. Header (Top Center):**
* A text box states: "Overall model is learned by repeating steps ② to ④."
**2. Main Diagram - Left Side (Client Column):**
* **Vertical Double-Headed Arrow (Labeled ①):** Positioned on the far left, spanning the height of the three client boxes. It is labeled with the circled number ① and the text "IDs matched between clients."
* **Client Boxes (A, B, C):** Three vertically stacked, identical blue-header boxes.
* **Client A:** Header text "Client A". Contains a blue cylinder labeled "Data" with a teal arrow pointing right to a neural network icon (a "Lower model").
* **Client B:** Header text "Client B". Same internal structure as Client A.
* **Client C:** Header text "Client C". Same internal structure as Client A.
* **Client Icons (Bottom Left):** Below the client boxes are three stylized human icons.
* Icon **II** is below Client C.
* Icon **III** is to the right of II, next to a globe/shield icon.
* A third, unlabeled icon is to the left of II.
**3. Main Diagram - Center (Process Flow & Active Client):**
* **Step ② Description (Top Center Box):** A text box reads: "②The same ID data is submitted between clients and each output of lower model is sent to the active client."
* **Data Vector (I):** Below the Step ② box, a vertical vector is shown: `[1.0, 2.1, -5.0, ...]`. It is labeled with the Roman numeral **I** and is associated with a blue human icon wearing glasses.
* **Active Client Box (Central Purple Box):** A large box with a purple header labeled "Active Client".
* **Step ③ Description:** Text inside reads: "③The output of each client is used as input to update upper model."
* **Input Data Vectors:** Three vectors are shown entering from the left, corresponding to outputs from Clients A, B, and C:
* Top vector: `[1.0, 2.1, -5.0, ...]` (matches vector I).
* Middle vector: `[3.6, -0.1, -8.5, ...]`.
* Bottom vector: `...` (ellipsis indicating continuation).
* **Neural Network & Secure Computation:** These vectors feed into a neural network icon. To its right is a blue shield icon with a padlock, labeled "Secure Computation".
* **Step ④ Description (Bottom Center):** Text reads: "④Propagate the error to each client and learn the lower model." A thick blue arrow curves from the "Secure Computation" output back towards the client column on the left.
**4. Main Diagram - Right Side (Model Architecture):**
* **Model Architecture Box:** A large rounded rectangle on the right.
* **"Lower model" Label:** At the top left inside the box.
* **Client-Specific Lower Models:** Three neural network icons are vertically aligned, labeled "Client A", "Client B", and "Client C".
* **"Upper model" Label:** At the top right inside the box.
* **Central Upper Model:** A single, larger neural network icon on the right.
* **Connections:** Gray arrows flow from each client's lower model icon to the central upper model icon, illustrating the aggregation of client outputs.
* **"Overall model" Label & Icon:** Below the model architecture box is a red silhouette of a human head with gears inside, labeled "Overall model".
### Detailed Analysis
The diagram explicitly details a four-step cyclic process:
1. **Step ① (ID Matching):** Clients (A, B, C) first align their datasets by matching user IDs. This is represented by the vertical arrow spanning the client column.
2. **Step ② (Data Submission & Lower Model Output):** Each client processes its local "Data" through its local "Lower model" neural network. The output vectors (e.g., `[1.0, 2.1, -5.0, ...]`) are sent to a designated "Active Client."
3. **Step ③ (Upper Model Update):** The "Active Client" collects the output vectors from all clients. These vectors serve as the input to update the central "Upper model." This update process is performed using "Secure Computation," ensuring privacy.
4. **Step ④ (Error Propagation & Lower Model Update):** The error from the updated upper model is propagated back to each individual client. Each client then uses this error signal to update its own local "Lower model."
The process is iterative, as stated in the header: "Overall model is learned by repeating steps ② to ④."
### Key Observations
* **Hierarchical Model Structure:** The architecture clearly separates client-specific "Lower models" from a centralized "Upper model." The "Overall model" is the composite result of this hierarchy.
* **Centralized Coordination via an "Active Client":** While the learning is federated, coordination and secure aggregation are handled by one client designated as "Active" for a given iteration.
* **Privacy-Preserving Mechanism:** The "Secure Computation" component (shield icon) is critically placed at the point where client data (in the form of model outputs) is aggregated to update the upper model, highlighting its role in protecting data privacy.
* **Bidirectional Data Flow:** The process involves a forward pass (client outputs to upper model) and a backward pass (error propagation from upper model to clients), mirroring backpropagation in a distributed setting.
* **Visual Consistency:** Neural network icons are used consistently to represent both lower and upper models. Blue arrows consistently indicate the primary flow of data and instructions.
### Interpretation
This diagram illustrates a **Vertical Federated Learning** or **Split Learning** paradigm. In this setup, different clients hold different features for the same set of users (enabled by Step ① ID matching). Each client's "Lower model" processes its private features into an intermediate representation (the output vectors). These representations, not the raw data, are sent to the "Active Client" and combined to train the "Upper model," which makes the final prediction.
The "Secure Computation" step is crucial; it implies techniques like homomorphic encryption, secure multi-party computation, or trusted execution environments are used to aggregate the client outputs without exposing them, thus preserving data privacy. The iterative nature (repeating steps ②-④) is how the entire distributed system converges to an optimal "Overall model."
The presence of multiple client icons (I, II, III) at the bottom may suggest different roles or instances across training rounds, with the "Active Client" role potentially rotating. The diagram effectively communicates a complex, privacy-conscious machine learning workflow, emphasizing the separation of data, the hierarchy of models, and the cyclic nature of distributed training.
DECODING INTELLIGENCE...