## Diagram: Closed-Source Tests Process Flow
### Overview
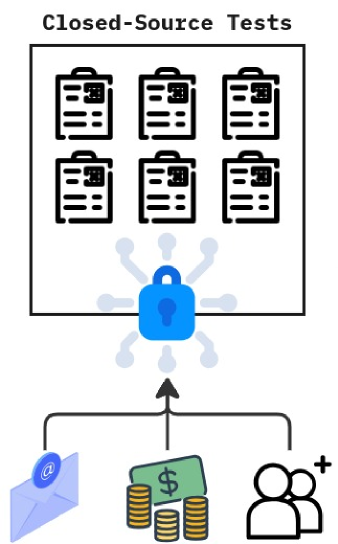
The image is a conceptual diagram illustrating a process or system related to "Closed-Source Tests." It depicts a flow where various resources or inputs are secured before being utilized within a set of closed, proprietary test documents. The visual style is a simple, flat icon-based illustration.
### Components/Axes
The diagram is organized vertically into three distinct regions:
1. **Header Region (Top):**
* **Title:** "Closed-Source Tests" is written in a bold, sans-serif font, centered at the very top.
* **Main Container:** A large, black-outlined rectangle dominates the upper half of the image. Inside this rectangle are six identical icons arranged in a 2x3 grid (two rows, three columns).
* **Icons:** Each icon is a black-and-white line drawing of a clipboard. On each clipboard, there is a stylized QR code in the upper-left corner and three horizontal lines representing text below it.
2. **Central Security Element (Middle):**
* **Padlock Icon:** Positioned centrally below the main rectangle is a large, blue padlock icon. It has a classic shape with a keyhole.
* **Radiating Lines:** Eight light-blue lines with circular endpoints radiate outward from the padlock, suggesting a network, data flow, or a protective field.
3. **Input/Resource Region (Bottom):**
* **Three Input Icons:** At the bottom of the diagram, three distinct icons are arranged horizontally.
* **Left:** A light blue envelope icon with a dark blue "@" symbol on its flap, representing email or electronic communication.
* **Center:** A green dollar bill icon with a "$" symbol, accompanied by three stacks of gold coins below it, representing financial resources or funding.
* **Right:** A black outline icon of two people (one slightly behind the other) with a small "+" symbol to the upper right, representing personnel, team members, or user accounts.
* **Flow Arrows:** A black arrow originates from the top of the central dollar/coins icon and points directly upward to the base of the blue padlock. From the padlock, a single black arrow points upward into the bottom of the large "Closed-Source Tests" rectangle. This establishes a clear directional flow: Inputs → Security → Tests.
### Detailed Analysis
* **Spatial Grounding:** The legend/title is at the top-center. The primary data (the six test documents) is contained within the top rectangle. The security mechanism (padlock) is centrally located, acting as a gateway. The input sources are anchored at the bottom.
* **Component Isolation:**
* **Header (Tests):** Contains six discrete, identical test document units. The QR codes imply each test may be uniquely identifiable or trackable.
* **Middle (Security):** The padlock is the focal point, visually connecting the inputs to the outputs. Its blue color makes it stand out against the black-and-white elements.
* **Footer (Inputs):** Clearly depicts three categories of resources required: communication/data (@), capital ($), and human resources (people+).
* **Flow Verification:** The arrows create a unidirectional, bottom-up flow. Resources are funneled into a secured system (the padlock), which then grants access to or enables the closed-source tests.
### Key Observations
1. **Security as a Gatekeeper:** The padlock is not just a symbol; it is an active component in the flow. All inputs must pass through it before reaching the tests.
2. **Proprietary Nature:** The title "Closed-Source Tests" and the secured container strongly imply that the test methodologies, data, or results are proprietary, confidential, or not publicly accessible.
3. **Resource Dependency:** The diagram explicitly shows that conducting these tests requires a combination of communication/information, financial investment, and personnel.
4. **Standardization:** The six test documents are visually identical, suggesting a standardized format or batch of tests being conducted under the same secured conditions.
### Interpretation
This diagram illustrates a **controlled and resource-intensive process for conducting proprietary evaluations.**
* **What it suggests:** The data or processes involved in these "Closed-Source Tests" are considered valuable or sensitive, necessitating a security layer (the padlock) to control access and integrity. The tests are not standalone; they are fueled by tangible inputs—information flow, money, and people.
* **Relationships:** The relationship is hierarchical and gated. Inputs are subordinate to the security protocol, which in turn is subordinate to the final test suite. The security element mediates the relationship between resources and the proprietary work.
* **Anomalies/Notable Points:** The use of QR codes on the test documents is a specific detail. It could indicate that each test instance is serialized, linked to a digital record, or requires scanning for access, further emphasizing control and tracking. The radiating lines from the padlock might symbolize that the security protocol actively monitors or manages connections to the tests, rather than being a passive barrier.
**In essence, the diagram maps a pipeline: Invest resources → Secure the process → Execute proprietary tests.** It visually argues that closed-source testing is a protected, resource-backed activity.