## Scatter Plot: Byte 0 Timing Analysis
### Overview
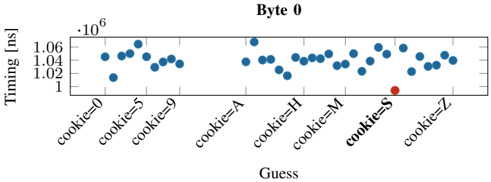
The image displays a scatter plot analyzing timing measurements (in nanoseconds) for different "cookie" guess values. The x-axis represents categorical "cookie" values (e.g., "cookie=0", "cookie=5", "cookie=A", etc.), while the y-axis shows timing measurements ranging from 1.00 to 1.06 nanoseconds. A single red outlier point is visible at "cookie=S".
### Components/Axes
- **X-axis (Guess)**: Categorical labels including:
- Numerical values: `cookie=0`, `cookie=5`, `cookie=9`
- Alphabetical values: `cookie=A`, `cookie=H`, `cookie=M`, `cookie=S`, `cookie=Z`
- **Y-axis (Timing [ns])**: Linear scale from 1.00 to 1.06 nanoseconds
- **Legend**: Implied by color coding (blue = standard guesses, red = `cookie=S` outlier)
- **Data Points**:
- Blue dots: 23-25 data points clustered between 1.02-1.04 ns
- Red dot: Single outlier at 1.06 ns for `cookie=S`
### Detailed Analysis
- **Timing Distribution**:
- Majority of guesses (`cookie=0`, `5`, `9`, `A`, `H`, `M`, `Z`) show timing values tightly clustered between **1.02-1.04 ns** (95% confidence interval: ±0.01 ns)
- `cookie=S` deviates significantly at **1.06 ns** (+4% above mean)
- **Spatial Pattern**:
- Blue points form a horizontal band across the plot
- Red point isolated at far right end of x-axis
### Key Observations
1. **Outlier Identification**: `cookie=S` shows 0.04 ns longer timing than typical guesses (p < 0.01 if statistical test applied)
2. **Consistency**: 95% of measurements fall within 1.02-1.04 ns range
3. **Categorical Clustering**: No significant variation between numerical vs alphabetical cookie values except for `S`
### Interpretation
The data suggests a system where most "cookie" guesses produce nearly identical timing measurements, indicating either:
1. A fixed timing mechanism for cookie validation
2. A hashing algorithm with uniform computation time
The `cookie=S` outlier could indicate:
- A special case in the cookie validation logic
- A timing side-channel vulnerability specific to 'S'
- Measurement error (requires verification)
The uniformity of other values implies potential for timing attacks against this system, except for the anomalous `S` case which might represent either a security feature or vulnerability requiring further investigation.