## Diagram: Data Compression Attack
### Overview
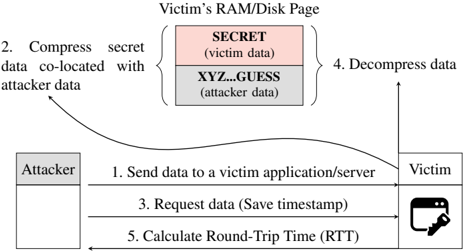
The image illustrates a data compression attack targeting a victim's RAM/Disk page. The diagram shows the steps involved, starting with the attacker sending data to the victim, compressing secret data co-located with attacker data, requesting data, decompressing data, and calculating the round-trip time.
### Components/Axes
* **Title:** Victim's RAM/Disk Page
* **Attacker:** A gray box on the left side of the diagram.
* **Victim:** A representation of a computer screen with a key icon in the bottom-right corner, located on the right side of the diagram.
* **Memory Block:** A stacked block representing the victim's RAM/Disk page, consisting of two sections:
* **SECRET (victim data):** Top section, colored light red.
* **XYZ...GUESS (attacker data):** Bottom section, colored light gray.
* **Steps:** Numbered steps indicating the flow of the attack.
### Detailed Analysis
1. **Send data to a victim application/server:** A horizontal arrow points from the "Attacker" to the "Victim".
2. **Compress secret data co-located with attacker data:** A curved arrow points from the "Attacker" to the memory block, specifically targeting both the "SECRET" and "XYZ...GUESS" sections.
3. **Request data (Save timestamp):** A horizontal arrow points from the "Victim" to the "Attacker".
4. **Decompress data:** A vertical arrow points upwards from the memory block.
5. **Calculate Round-Trip Time (RTT):** A horizontal arrow points from the "Attacker" to the "Victim".
### Key Observations
* The attacker manipulates the victim's memory by co-locating their data with the victim's secret data.
* The attack involves compressing and decompressing data, likely to exploit vulnerabilities in the compression algorithm or the way the data is handled.
* The round-trip time is calculated, suggesting that timing analysis is part of the attack strategy.
### Interpretation
The diagram depicts a sophisticated attack where the attacker attempts to extract secret information from the victim's memory by manipulating data compression. The attacker first sends data to the victim, then influences the compression process by co-locating their data with the victim's secret data. By requesting the data and measuring the round-trip time, the attacker can potentially infer information about the compressed data and, ultimately, the secret data itself. This type of attack exploits vulnerabilities related to data compression and timing analysis to compromise the victim's system.