## Diagram: Cyber Attack Exploiting Co-Located Data in Memory
### Overview
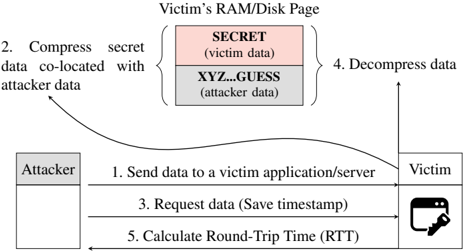
This diagram illustrates a memory-based side-channel attack where an attacker exploits co-located data in a victim's RAM/disk page. The attack involves compressing secret data with attacker-controlled data, then inferring the secret through timing analysis of round-trip time (RTT) measurements.
### Components/Axes
- **Entities**:
- **Attacker**: Initiates the attack sequence
- **Victim**: Target system/application
- **Victim's RAM/Disk Page**: Memory region containing:
- **SECRET (victim data)**: Pink-colored box (top section)
- **XYZ...GUESS (attacker data)**: Gray-colored box (bottom section)
- **Process Flow**:
1. **Send data to victim application/server** (Attacker → Victim)
2. **Compress secret data co-located with attacker data** (RAM/Disk Page)
3. **Request data (Save timestamp)** (Victim → Attacker)
4. **Decompress data** (Victim)
5. **Calculate Round-Trip Time (RTT)** (Attacker)
- **Visual Elements**:
- Arrows indicate data flow direction
- Color coding distinguishes data types:
- Pink = Victim's secret data
- Gray = Attacker's data
- Key icon represents the Victim's system
### Detailed Analysis
1. **Data Co-Location**: Secret data (pink) is stored adjacent to attacker-controlled data (gray) in the same memory page.
2. **Compression Step**: Secret data is compressed alongside attacker data, creating a mixed data block.
3. **Timing Attack Mechanism**:
- Attacker sends data to victim
- Victim processes request and saves timestamp
- Attacker measures RTT to infer secret data characteristics
4. **Decompression**: Victim decompresses data after receiving request
### Key Observations
- The attack relies on precise timing measurements (RTT) to infer secret data
- Color coding visually separates victim/attacker data regions
- Memory page segmentation shows attacker's data guessing mechanism ("XYZ...GUESS")
- Process flow follows a clear sequential pattern (1→2→3→4→5)
### Interpretation
This diagram demonstrates a sophisticated memory-based attack vector:
1. **Data Proximity Exploitation**: Attackers leverage physical memory co-location to create side-channel vulnerabilities
2. **Timing as a Leakage Vector**: RTT measurements reveal information about secret data compression patterns
3. **Compression as Attack Vector**: The compression/decompression process becomes a attack surface rather than a security measure
4. **Memory Page Segmentation**: The "XYZ...GUESS" section suggests attacker attempts to predict or manipulate adjacent memory contents
The attack flow reveals how seemingly benign operations (data compression, RTT measurement) can be weaponized to extract sensitive information. This highlights the importance of memory isolation techniques and constant-time programming practices to mitigate such side-channel attacks.