## Diagram: Secure Computation for Feature Similarity
### Overview
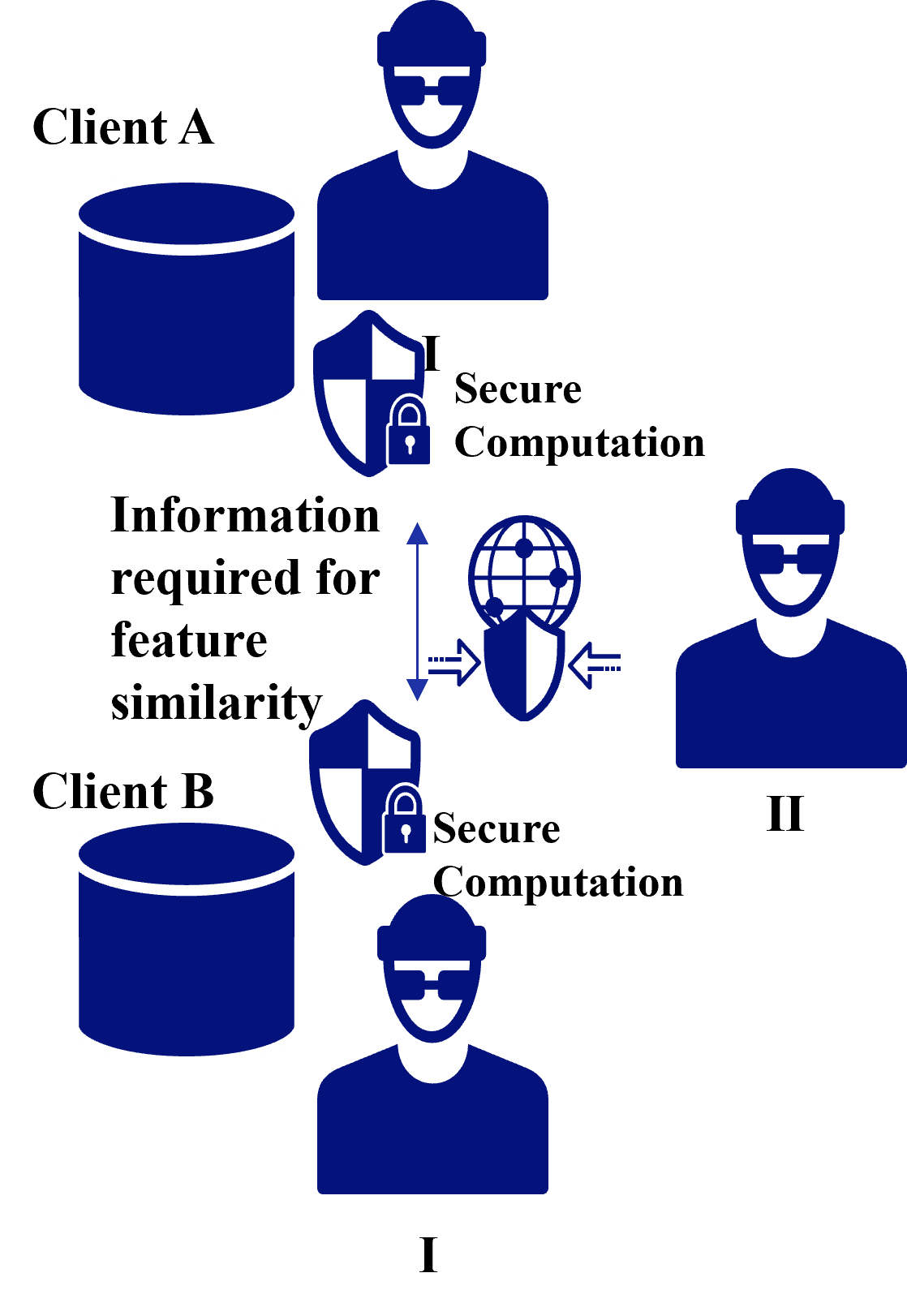
The image illustrates a secure computation process for determining feature similarity between two clients (Client A and Client B). The diagram highlights the flow of information and the involvement of secure computation entities.
### Components/Axes
* **Clients:** Client A (top-left) and Client B (bottom-left), each represented by a database icon and a person icon.
* **Secure Computation Entities:** Two entities labeled "I" (bottom) and "II" (right), each represented by a person icon.
* **Secure Computation Blocks:** Two blocks labeled "Secure Computation" associated with each client, represented by a shield icon with a padlock.
* **Information Flow:** Arrows indicate the flow of "Information required for feature similarity" from both clients to a central secure computation block.
* **Central Secure Computation Block:** A shield icon with a globe inside, positioned between the two clients.
### Detailed Analysis
* **Client A:** Located at the top-left. It consists of a database icon and a person icon.
* **Client B:** Located at the bottom-left. It consists of a database icon and a person icon.
* **Information Flow:** The text "Information required for feature similarity" is positioned between the two clients. A double-headed arrow points upwards from Client B and downwards from Client A towards a central shield icon with a globe inside. Two arrows point from the central shield icon to the right.
* **Secure Computation Blocks:** Each client has a "Secure Computation" block associated with it, represented by a shield icon with a padlock.
* **Secure Computation Entities:** Two entities labeled "I" and "II" are present. Entity "I" is located below Client B, and Entity "II" is located to the right of Client A. Each entity is represented by a person icon.
### Key Observations
* The diagram emphasizes the secure exchange of information between clients and secure computation entities.
* The central secure computation block acts as an intermediary for processing information from both clients.
* The presence of "Secure Computation" blocks near each client suggests that some computation is performed locally before sending information to the central block.
### Interpretation
The diagram illustrates a secure multi-party computation (MPC) scenario where two clients want to determine the similarity of their features without revealing the actual features to each other or to a single third party. The "Secure Computation" blocks likely represent cryptographic protocols that ensure the privacy of the data during computation. The central secure computation block performs the similarity calculation based on the encrypted or masked data received from the clients. The entities "I" and "II" could represent different parties involved in the secure computation protocol, such as data providers or computation servers. The diagram highlights the importance of secure computation in protecting sensitive information while still enabling collaborative analysis.