## Diagram: Secure Multi-Party Computation Workflow
### Overview
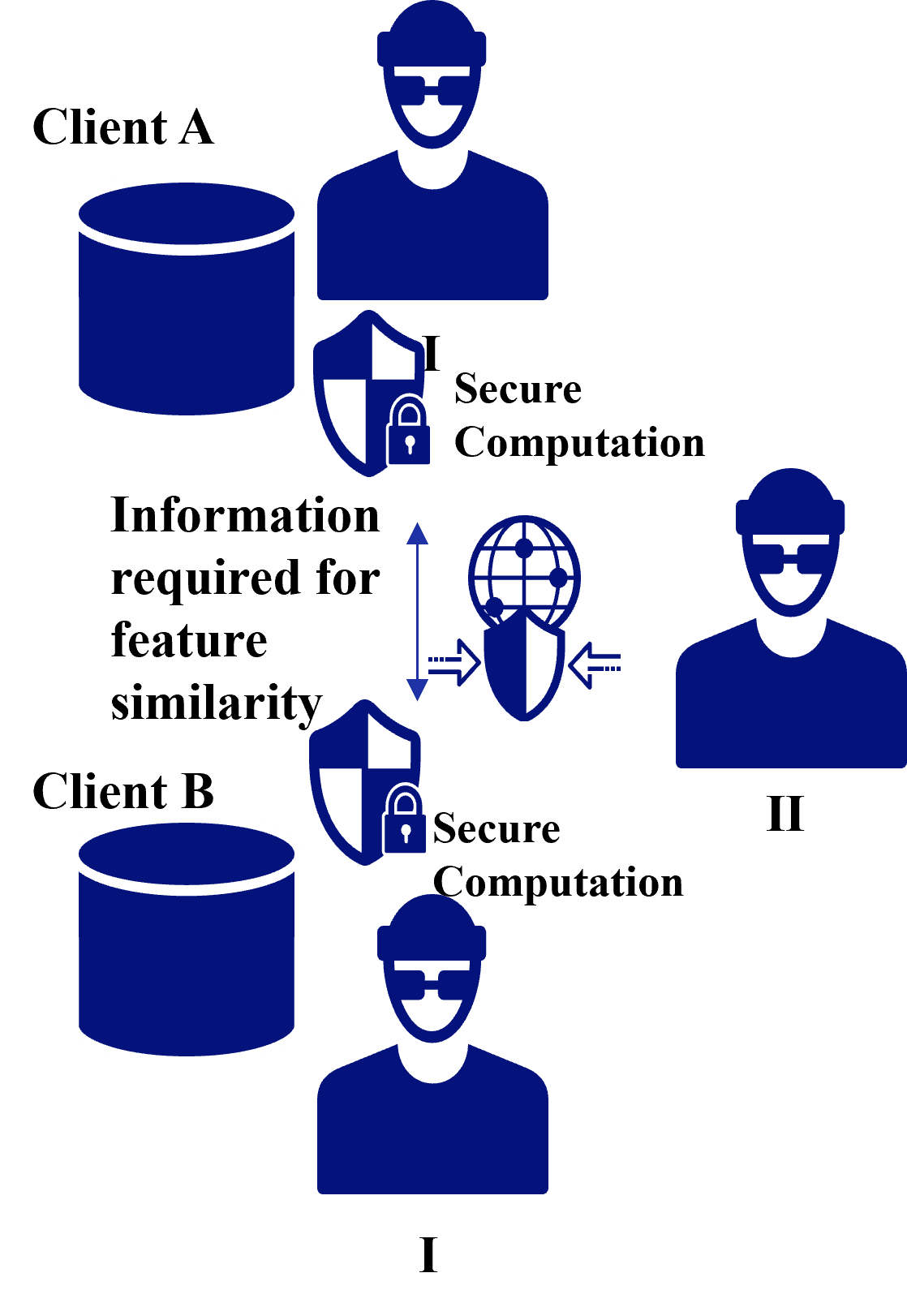
The diagram illustrates a secure computation process between two clients (Client A and Client B) involving encrypted data exchange and feature similarity analysis. It uses symbolic representations (shields, locks, arrows) to depict secure information flow.
### Components/Axes
- **Clients**:
- **Client A**: Positioned at the top-left, represented by a blue silhouette with a hoodie and sunglasses.
- **Client B**: Positioned at the bottom-left, identical visual representation to Client A.
- **Data Stores**:
- **Database A**: A blue cylinder with a white outline, adjacent to Client A.
- **Database B**: A blue cylinder with a white outline, adjacent to Client B.
- **Secure Computation**:
- Two shield icons with padlocks labeled "Secure Computation" (one near Client A, one near Client B).
- **Information Flow**:
- Arrows connecting the shields, labeled "Information required for feature similarity."
- A globe icon with grid lines and dots, positioned between the shields, symbolizing encrypted data transmission.
- **Legend**:
- No explicit legend present, but symbols are standardized:
- **Shield + Lock**: Represents secure computation.
- **Arrows**: Indicate data flow direction.
- **Globe**: Symbolizes encrypted data transmission.
### Detailed Analysis
- **Client A and Client B**: Both clients are visually identical, suggesting symmetric roles in the process.
- **Secure Computation**: The shields with locks are placed symmetrically, indicating mutual participation in the secure process.
- **Information Flow**:
- The text "Information required for feature similarity" is centrally located, emphasizing its role as the core data exchanged.
- Arrows point bidirectionally between the shields, implying mutual exchange of encrypted data.
- The globe icon bridges the shields, reinforcing the idea of secure, encrypted communication.
### Key Observations
1. **Symmetry**: The diagram emphasizes equal roles for both clients in the secure computation process.
2. **Encryption Focus**: The repeated use of shields and locks highlights data privacy and security as central themes.
3. **Feature Similarity**: The explicit label indicates the purpose of the data exchange—comparing features while maintaining confidentiality.
### Interpretation
This diagram represents a **secure multi-party computation (MPC)** framework where two clients collaborate to analyze feature similarity without exposing raw data. The shields and locks symbolize cryptographic techniques (e.g., homomorphic encryption or secure enclaves) that protect data during processing. The bidirectional arrows and globe icon suggest a decentralized, trustless environment where neither client has direct access to the other’s data.
The absence of a traditional legend implies the diagram relies on universally recognized symbols (e.g., shields for security, arrows for flow). The central placement of "Information required for feature similarity" underscores its importance as the actionable outcome of the secure computation.
This setup is critical in privacy-preserving machine learning, where clients must collaborate on model training or analysis without compromising sensitive data. The diagram abstracts the technical complexity (e.g., cryptographic protocols) into a high-level workflow, making it accessible for stakeholders focused on data governance or system design.