## Flowchart: Speculative Execution Vulnerability Categories
### Overview
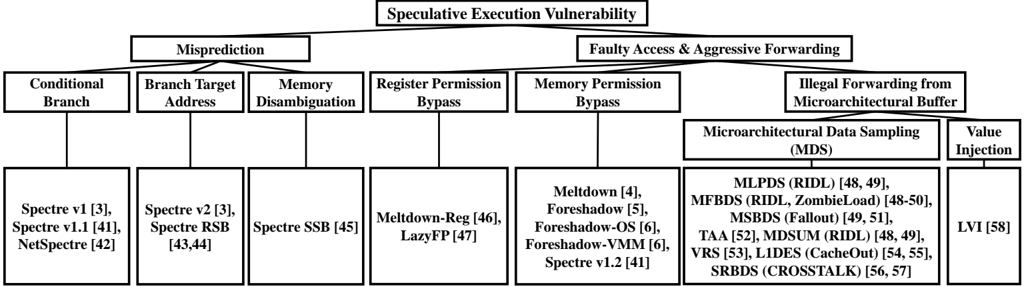
The diagram illustrates a hierarchical taxonomy of speculative execution vulnerabilities, branching into two primary categories: **Misprediction** and **Faulty Access & Aggressive Forwarding**. Each category contains subcategories with specific vulnerability examples and references.
### Components/Axes
- **Main Title**: "Speculative Execution Vulnerability"
- **Primary Branches**:
1. **Misprediction**
- Conditional Branch
- Branch Target Address
- Memory Disambiguation
- Register Permission Bypass
2. **Faulty Access & Aggressive Forwarding**
- Memory Permission Bypass
- Microarchitectural Data Sampling (MDS)
- Value Injection
### Detailed Analysis
#### Misprediction Branch
- **Conditional Branch**:
- Spectre v1 [3], Spectre v1.1 [41], NetSpectre [42]
- **Branch Target Address**:
- Spectre v2 [3], Spectre RSB [43,44]
- **Memory Disambiguation**:
- Spectre SSB [45]
- **Register Permission Bypass**:
- Meltdown-Reg [46], LazyFP [47]
#### Faulty Access & Aggressive Forwarding Branch
- **Memory Permission Bypass**:
- Meltdown [4], Foreshadow [5], Foreshadow-OS [6], Foreshadow-VMM [6], Spectre v1.2 [41]
- **Microarchitectural Data Sampling (MDS)**:
- MLPDS (RIDL) [48,49], MFBDS (RIDL, ZombieLoad) [48-50], MSBDS (Fallout) [49,51], TAA [52], MDSUM (RIDL) [48,49], VRS [53], L1DES (CacheOut) [54,55], SRBDS (CROSSSTALK) [56,57]
- **Value Injection**:
- LVI [58]
### Key Observations
1. **Misprediction Dominance**: The "Misprediction" branch contains 4 subcategories, each with 2-3 vulnerabilities, suggesting a focus on branch prediction flaws.
2. **MDS Proliferation**: The MDS subcategory lists 8 distinct vulnerabilities, indicating it is the most extensively exploited category.
3. **Cross-Referencing**: Some vulnerabilities (e.g., Spectre v1.2, Meltdown) appear in both branches, highlighting overlapping attack vectors.
4. **Temporal Clustering**: Vulnerabilities are grouped by discovery timelines (e.g., Spectre v1/v2, Meltdown), reflecting historical progression.
### Interpretation
This taxonomy reveals that speculative execution vulnerabilities primarily exploit **branch prediction errors** (Misprediction) and **memory access bypasses** (Faulty Access). The MDS category stands out as the most diverse, encompassing side-channel attacks like RIDL and CacheOut. The overlap of vulnerabilities (e.g., Spectre v1.2 in both branches) underscores the interconnected nature of these flaws. The diagram emphasizes the need for defenses targeting both architectural mispredictions and microarchitectural data leakage, with LVI representing a unique class of value-based attacks. The hierarchical structure aids in categorizing mitigation strategies, such as Spectre mitigations (SSB, RSB) versus MDS-specific countermeasures (e.g., RIDL patches).