TECHNICAL ASSET FINGERPRINT
e461809c6eccc7cb85175f12
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
## System Diagram: Privacy-Preserving Robust Model Aggregation
### Overview
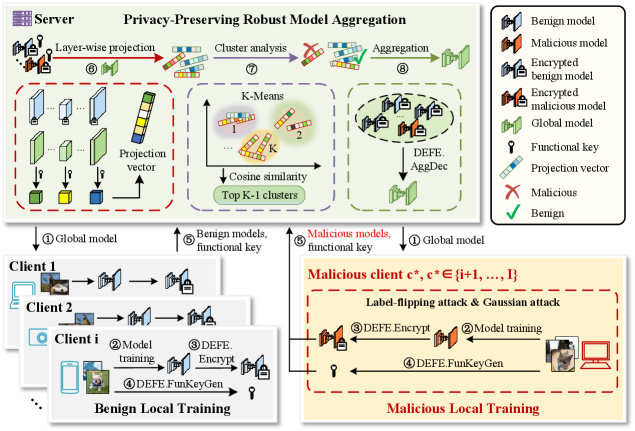
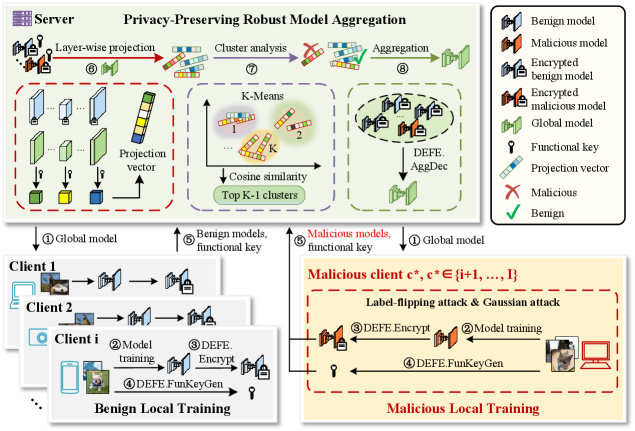
The image is a system diagram illustrating a privacy-preserving robust model aggregation scheme. It depicts the interaction between a server and multiple clients (both benign and malicious) during a federated learning process. The diagram highlights the steps involved in model training, encryption, aggregation, and security measures against malicious attacks.
### Components/Axes
* **Title:** Privacy-Preserving Robust Model Aggregation
* **Server:** Represents the central server in the federated learning system.
* **Clients:** Represent individual clients participating in the training process. There are benign clients and malicious clients.
* **Benign Local Training:** Represents the process of training models on benign clients.
* **Malicious Local Training:** Represents the process of training models on malicious clients, including attack mechanisms.
* **Legend (Top-Right):**
* Benign model (Blue house icon)
* Malicious model (Red house icon)
* Encrypted benign model (Blue house icon with lock)
* Encrypted malicious model (Red house icon with lock)
* Global model (Green house icon)
* Functional key (Key icon)
* Projection vector (Blue/White bars)
* Malicious (Red X)
* Benign (Green Checkmark)
### Detailed Analysis
**Server-Side Processing (Top):**
1. **Layer-wise projection (6):** The server receives model updates from clients and applies layer-wise projection.
* Input: Model updates from clients.
* Process: Applies layer-wise projection.
* Output: Projected model updates.
2. **Cluster analysis (7):** The server performs cluster analysis on the projected model updates using K-Means.
* Input: Projected model updates.
* Process: K-Means clustering.
* Output: Clusters of model updates.
* **K-Means:**
* Clusters labeled 1, 2, ..., K.
* Cosine similarity is used to determine cluster membership.
* Top K-1 clusters are selected.
3. **Aggregation (8):** The server aggregates the selected clusters using DEFE.AggDec.
* Input: Selected clusters.
* Process: Aggregation using DEFE.AggDec.
* Output: Updated global model.
**Client-Side Processing (Bottom):**
1. **Benign Local Training (Left):**
* **Client 1, Client 2, Client i:** Represent individual benign clients.
* **Model training (2):** Clients train models locally using their data.
* Input: Local data.
* Process: Model training.
* Output: Trained model.
* **DEFE.Encrypt (3):** Clients encrypt their trained models using DEFE.Encrypt.
* Input: Trained model.
* Process: Encryption.
* Output: Encrypted model.
* **DEFE.FunKeyGen (4):** Clients generate functional keys using DEFE.FunKeyGen.
* Input: N/A
* Process: Key generation.
* Output: Functional key.
* **Global model (1):** The server sends the global model to the clients.
* **Benign models, functional key (5):** Clients send their encrypted models and functional keys to the server.
2. **Malicious Local Training (Right):**
* **Malicious client c*, c* ∈ {i+1, ..., I}:** Represents a malicious client.
* **Label-flipping attack & Gaussian attack:** The malicious client performs label-flipping and Gaussian attacks.
* **Model training (2):** The malicious client trains a model locally.
* Input: Local data.
* Process: Model training.
* Output: Trained model.
* **DEFE.Encrypt (3):** The malicious client encrypts the trained model using DEFE.Encrypt.
* Input: Trained model.
* Process: Encryption.
* Output: Encrypted model.
* **DEFE.FunKeyGen (4):** The malicious client generates a functional key using DEFE.FunKeyGen.
* Input: N/A
* Process: Key generation.
* Output: Functional key.
* **Global model (1):** The server sends the global model to the malicious client.
* **Malicious models, functional key (5):** The malicious client sends the encrypted model and functional key to the server.
### Key Observations
* The diagram illustrates a federated learning system with privacy-preserving mechanisms.
* Benign clients train models and encrypt them before sending them to the server.
* Malicious clients can perform attacks such as label-flipping and Gaussian attacks.
* The server uses K-Means clustering and DEFE.AggDec to aggregate model updates and mitigate the impact of malicious attacks.
### Interpretation
The diagram presents a system designed to address the challenges of privacy and robustness in federated learning. By encrypting model updates and employing robust aggregation techniques, the system aims to protect client data privacy and mitigate the impact of malicious attacks. The use of K-Means clustering allows the server to identify and potentially isolate malicious model updates, while DEFE.AggDec provides a mechanism for aggregating the remaining updates in a robust manner. The system highlights the importance of considering both privacy and security in federated learning deployments.
DECODING INTELLIGENCE...
EXPERT: gemma-3-27b-it-free VERSION 1
RUNTIME: google-free/gemma-3-27b-it
INTEL_VERIFIED
\n
## Diagram: Privacy-Preserving Robust Model Aggregation
### Overview
This diagram illustrates a system for privacy-preserving robust model aggregation, involving a server and multiple clients. It details the process of local model training on clients, secure aggregation on the server, and the handling of potentially malicious clients. The diagram is divided into three main sections: Server-side processing (top), Benign Local Training (bottom-left), and Malicious Local Training (bottom-right). The entire process is framed under the title "Privacy-Preserving Robust Model Aggregation".
### Components/Axes
The diagram uses several visual components to represent data and processes:
* **Models:** Represented as rectangular prisms, with different colors indicating their status (Benign, Malicious, Encrypted).
* **Functional Keys:** Represented as key icons.
* **Projection Vectors:** Represented as arrows.
* **Clusters:** Represented as numbered groups (1, 2, K).
* **Arrows:** Indicate the flow of data and processes.
* **Boxes:** Delineate different stages or sections of the process.
* **Labels:** Numbered labels (1-8) guide the flow of the process.
The legend (top-right) defines the color coding:
* **Green:** Benign model
* **Red:** Malicious model
* **Green with a lock:** Encrypted benign model
* **Red with a lock:** Encrypted malicious model
* **Blue:** Global model
* **Key Icon:** Functional key
* **Arrow:** Projection vector
* **Red X:** Malicious
* **Green Circle:** Benign
### Detailed Analysis or Content Details
**Server-Side Processing (Top Section):**
1. **Global Model (①):** A blue rectangular prism representing the initial global model.
2. **Layer-wise Projection (⑥):** The global model is projected into multiple projection vectors (arrows). Each projection vector is associated with a rectangular prism, colored to indicate whether it's a benign or malicious model.
3. **Cluster Analysis (⑦):** The projection vectors are fed into a K-Means clustering algorithm. The diagram shows two clusters labeled "1" and "2", with "Top K-1 clusters" indicated below. Cosine similarity is used for clustering.
4. **Aggregation (⑧):** The clusters are aggregated, resulting in a new set of models. These models are then decrypted using "DEFE\_AggDec". The resulting models are blue (global model).
**Benign Local Training (Bottom-Left Section):**
1. **Client 1, Client 2, Client i (①):** Represent multiple clients participating in the training process.
2. **Model Training (②):** Each client trains a local model.
3. **DEFE\_Encrypt (③):** The trained model is encrypted using "DEFE\_Encrypt".
4. **DEFE\_FunKeyGen (④):** A functional key is generated.
**Malicious Local Training (Bottom-Right Section):**
1. **Malicious client c*, c* {i+1, ... , I} (⑤):** Represents malicious clients.
2. **Model Training (⑥):** Malicious clients train models, potentially using "Label-flipping attack & Gaussian attack".
3. **DEFE\_Encrypt (⑦):** The trained model is encrypted using "DEFE\_Encrypt".
4. **DEFE\_FunKeyGen (⑧):** A functional key is generated.
### Key Observations
* The system distinguishes between benign and malicious clients.
* Encryption is used to protect the privacy of the local models.
* The server aggregates the models from multiple clients.
* K-Means clustering is used to identify and potentially mitigate the impact of malicious models.
* The "DEFE" modules (DEFE\_Encrypt, DEFE\_AggDec, DEFE\_FunKeyGen) play a crucial role in the privacy-preserving and robust aggregation process.
* The malicious client section explicitly mentions "Label-flipping attack & Gaussian attack", indicating the types of attacks the system is designed to handle.
### Interpretation
This diagram depicts a federated learning system designed to be robust against malicious participants. The core idea is to allow clients to train models locally, encrypt them, and send them to a central server for aggregation. The server uses techniques like K-Means clustering and functional keys to identify and mitigate the influence of malicious models. The "DEFE" modules likely implement differential privacy or other privacy-enhancing technologies to protect the data and models during the aggregation process.
The use of K-Means suggests that the server attempts to group similar models together, potentially identifying outliers (malicious models) that deviate significantly from the norm. The functional keys likely provide a mechanism for secure aggregation, ensuring that the server can combine the models without learning the individual client's data.
The explicit mention of "Label-flipping attack & Gaussian attack" highlights the system's focus on defending against common adversarial attacks in federated learning. The diagram suggests a layered approach to security, combining encryption, clustering, and functional keys to achieve both privacy and robustness. The entire system is designed to allow for collaborative model training while protecting the privacy of individual clients and ensuring the integrity of the aggregated model.
DECODING INTELLIGENCE...
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
## Diagram: Privacy-Preserving Robust Model Aggregation System
### Overview
This image is a technical system architecture diagram illustrating a **Privacy-Preserving Robust Model Aggregation** protocol for federated learning. It details the interaction between a central server and multiple clients (both benign and malicious), focusing on a secure aggregation process that uses encryption, clustering, and projection techniques to defend against model poisoning attacks (specifically label-flipping and Gaussian attacks). The diagram is divided into distinct regions: a Server process (top), Benign Local Training (bottom-left), and Malicious Local Training (bottom-right).
### Components/Axes
The diagram is organized into three primary spatial regions:
1. **Top Region: Server Process**
* **Title:** "Server Privacy-Preserving Robust Model Aggregation"
* **Components (Left to Right):**
* **Step ⑥ Layer-wise projection:** Shows model layers being processed into a "Projection vector".
* **Step ⑦ Cluster analysis:** Depicts a "K-Means" clustering process using "Cosine similarity" to find "Top K-1 clusters".
* **Step ⑧ Aggregation:** Illustrates the aggregation of models into a "Global model" using "DEFE: AggDec".
* **Legend (Top-Right Corner):** A box defining the symbols used throughout the diagram.
* `Benign model` (Green brain icon)
* `Malicious model` (Red brain icon)
* `Encrypted benign model` (Green brain with lock)
* `Encrypted malicious model` (Red brain with lock)
* `Global model` (Green brain with globe)
* `Functional key` (Key icon)
* `Projection vector` (Multi-colored bar)
* `Malicious` (Red X)
* `Benign` (Green checkmark)
2. **Bottom-Left Region: Benign Local Training**
* **Title:** "Benign Local Training"
* **Components:** Shows a stack of clients (Client 1, Client 2, Client i).
* **Process Flow (Numbered Steps):**
* ① `global model` (received from server)
* ② `Model training`
* ③ `DEFE: Encrypt`
* ④ `DEFE: FunKeyGen` (generates a `Functional key`)
* ⑤ `Benign models, functional key` (sent to server)
3. **Bottom-Right Region: Malicious Local Training**
* **Title:** "Malicious Local Training"
* **Subtitle:** "Malicious client `c*`, `c* ∈ {j+1, ..., I}`"
* **Attack Description:** "Label-flipping attack & Gaussian attack"
* **Process Flow (Numbered Steps):**
* ① `Global model` (received from server)
* ② `Model training` (with attack applied)
* ③ `DEFE: Encrypt`
* ④ `DEFE: FunKeyGen` (generates a `Functional key`)
* ⑤ `Malicious models, functional key` (sent to server)
### Detailed Analysis
The diagram outlines an 8-step server-side process that interacts with client-side training:
**Server-Side Workflow (Top Region):**
1. The server initiates the process by sending the `Global model` (Step ①) to all clients.
2. It receives models and keys from clients (Steps ⑤).
3. **Step ⑥ - Layer-wise projection:** The received models undergo a projection operation, resulting in a `Projection vector`. This is likely a dimensionality reduction or feature extraction step.
4. **Step ⑦ - Cluster analysis:** The projected vectors are clustered using `K-Means` based on `Cosine similarity`. The goal is to identify the `Top K-1 clusters`, presumably to isolate potentially malicious model updates.
5. **Step ⑧ - Aggregation:** The models from the identified benign clusters are aggregated using a function labeled `DEFE: AggDec` to produce an updated `Global model`. This new global model is then sent back to clients (Step ①), completing the cycle.
**Client-Side Workflow (Bottom Regions):**
* **Benign Clients:** Follow a standard secure training protocol: receive global model -> train locally -> encrypt model (`DEFE: Encrypt`) -> generate a functional key (`DEFE: FunKeyGen`) -> send encrypted model and key to server.
* **Malicious Clients:** Follow a similar technical flow but with a critical difference: their `Model training` (Step ②) incorporates a `Label-flipping attack & Gaussian attack`. Their output is a poisoned model, which is then encrypted and sent to the server alongside a functional key, mimicking the benign clients' communication pattern.
### Key Observations
1. **Symmetry in Communication:** Both benign and malicious clients perform identical post-training steps (encryption, key generation). This makes it difficult for the server to distinguish them based on communication protocol alone.
2. **Centralized Defense Mechanism:** The core defense lies entirely within the server's `Cluster analysis` (Step ⑦). The system assumes that malicious model updates will be statistically different enough (after projection) to form separate clusters, allowing the server to exclude them (`Top K-1 clusters`) before aggregation.
3. **Attack Specification:** The diagram explicitly names two attack vectors: `Label-flipping attack` (changing training data labels) and `Gaussian attack` (adding Gaussian noise to model updates).
4. **Notation:** The malicious client is denoted mathematically as `c*`, belonging to a set `{j+1, ..., I}`, suggesting a system with `I` total clients where the last `I-j` clients are malicious.
### Interpretation
This diagram presents a **defense-in-depth strategy for federated learning**. It addresses two critical challenges simultaneously:
* **Privacy:** Achieved through the `DEFE` (likely an acronym for a specific encryption scheme) processes (`Encrypt`, `FunKeyGen`, `AggDec`), which ensure the server cannot inspect raw model updates.
* **Robustness:** Achieved through the `Layer-wise projection` and `K-Means clustering` pipeline. The core hypothesis is that malicious model updates, even when encrypted, will project into a different region of the feature space than benign ones. By clustering in this space and aggregating only the largest cluster(s) (`Top K-1`), the server can dilute or exclude the influence of poisoned models.
The system's effectiveness hinges on the assumption that the projection and clustering can reliably separate benign from malicious updates *without* decrypting them. The inclusion of a `Functional key` for each client suggests it may be used in the secure aggregation decryption process (`AggDec`) or to verify client authenticity. The diagram effectively communicates a complex, multi-stage protocol where privacy and security are interwoven rather than treated as separate concerns.
DECODING INTELLIGENCE...
EXPERT: nemotron-free VERSION 1
RUNTIME: free/nvidia/nemotron-nano-12b-v2-vl:free
INTEL_VERIFIED
## Diagram: Privacy-Preserving Robust Model Aggregation System
### Overview
The diagram illustrates a decentralized machine learning system where multiple clients (benign and malicious) train local models, which are aggregated into a global model by a central server. The system emphasizes privacy preservation through encryption, functional keys, and robust aggregation techniques to mitigate malicious attacks.
### Components/Axes
1. **Server Section**:
- **Title**: "Privacy-Preserving Robust Model Aggregation"
- **Steps**:
- **6**: Layer-wise projection → Projection vectors (colored bars: green, yellow, blue).
- **7**: Cluster analysis using K-Means → Cosine similarity metric → Top K-1 clusters.
- **8**: Aggregation → DEFE.AggDec (decryption/aggregation process).
- **Legend**:
- **Benign model** (blue), **Malicious model** (orange), **Encrypted benign/malicious models** (locked icons), **Functional key** (key icon), **Projection vector** (bar chart), **Malicious** (red X), **Benign** (green check).
2. **Client Sections**:
- **Benign Clients (1, 2, i)**:
- **Steps**:
- **2**: Model training (images → screens → locked models).
- **3**: DEFE.Encrypt (encryption process).
- **4**: DEFE.FunKeyGen (functional key generation).
- **Flow**: Local training → Encryption → Functional key generation → Server.
- **Malicious Client (c*)**:
- **Label**: "Malicious client c*, c* ∈ {i+1, ..., I}"
- **Attacks**: Label-flipping attack & Gaussian attack.
- **Steps**:
- **3**: DEFE.Encrypt (malicious encryption).
- **2**: Model training (with attacks).
- **4**: DEFE.FunKeyGen (malicious key generation).
- **Flow**: Malicious training → Encryption → Functional key generation → Server.
### Detailed Analysis
- **Server Workflow**:
1. **Layer-wise projection** (Step 6): Clients project model parameters into vectors (colored bars), which are sent to the server.
2. **Cluster analysis** (Step 7): Server groups projection vectors into clusters using K-Means, prioritizing top K-1 clusters to reduce noise.
3. **Aggregation** (Step 8): DEFE.AggDec decrypts and aggregates models, ensuring robustness against malicious inputs.
- **Client Workflow**:
- **Benign Clients**: Train models locally, encrypt them with DEFE.Encrypt, and generate functional keys (DEFE.FunKeyGen) to enable secure aggregation.
- **Malicious Clients**: Perform label-flipping/Gaussian attacks during training, encrypt models, and generate functional keys. Their malicious models are flagged in the legend (red X).
- **Security Mechanisms**:
- **Encryption**: All models (benign/malicious) are encrypted before transmission (locked icons).
- **Functional Keys**: Generated via DEFE.FunKeyGen, used to decrypt models during aggregation.
- **Robust Aggregation**: Server focuses on top K-1 clusters to minimize the impact of malicious models.
### Key Observations
1. **Malicious Client Isolation**: Malicious clients are visually separated (orange box) and labeled with attacks (label-flipping/Gaussian).
2. **Encryption Consistency**: All models (benign/malicious) use DEFE.Encrypt, but malicious models are flagged post-aggregation.
3. **Key Generation**: Functional keys (DEFE.FunKeyGen) are critical for decryption, ensuring only valid models contribute to the global model.
4. **Cluster Prioritization**: Server discards outliers (bottom clusters) via K-Means, focusing on top K-1 clusters for aggregation.
### Interpretation
The system balances decentralization and security by:
- **Privacy Preservation**: Encrypting models and using functional keys to prevent exposure of raw data.
- **Robustness**: Aggregating only top clusters to mitigate malicious inputs, ensuring the global model remains accurate despite attacks.
- **Decentralization**: Clients retain control over local training, reducing central points of failure.
The diagram highlights a trade-off between computational overhead (encryption/key generation) and security, emphasizing that robust aggregation (via clustering and decryption) is essential for trustworthy federated learning in adversarial environments.
DECODING INTELLIGENCE...