\n
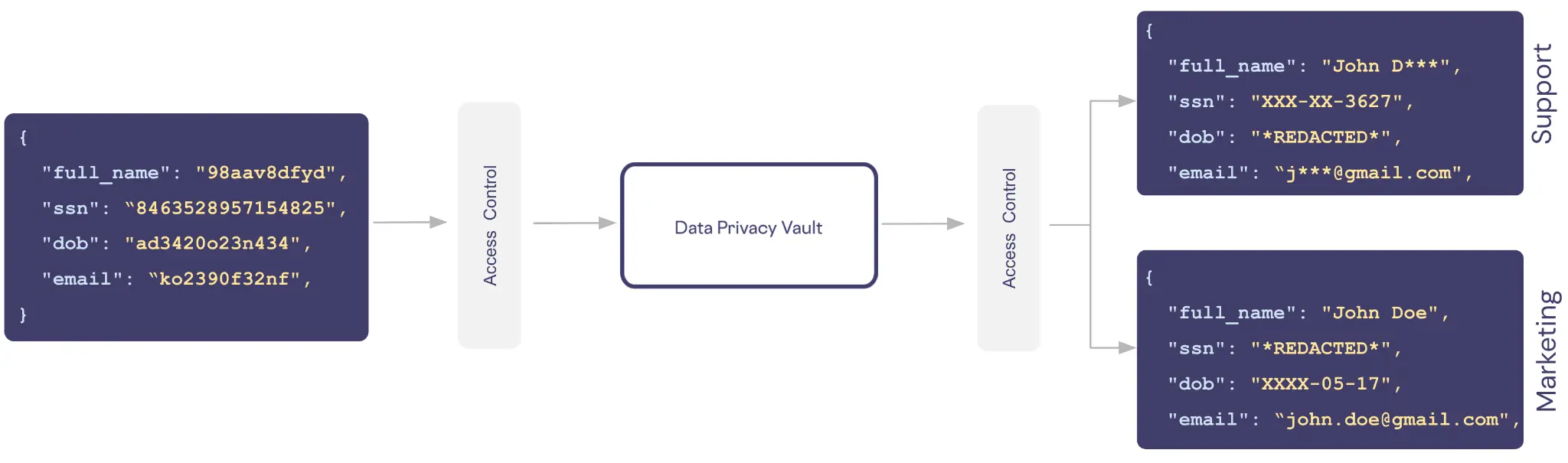
## Diagram: Data Privacy Vault Access Flow
### Overview
The image depicts a diagram illustrating data access flow to a "Data Privacy Vault" from two sources: a source labeled with a hexadecimal string and another labeled "Support" and "Marketing". The diagram highlights access control mechanisms and the types of data shared.
### Components/Axes
The diagram consists of three main rectangular components:
1. **Source 1:** A rectangular block on the left side containing JSON-formatted data.
2. **Data Privacy Vault:** A central, larger rectangular block labeled "Data Privacy Vault".
3. **Destination 1 & 2:** Two rectangular blocks on the right side, labeled "Support" (top) and "Marketing" (bottom), also containing JSON-formatted data.
Arrows with the label "Access Control" indicate the flow of data from the sources to the vault and from the vault to the destinations.
### Detailed Analysis or Content Details
**Source 1 (Left):**
The JSON data contains the following fields:
* `"full_name"`: `"98aav8dfyd"`
* `"ssn"`: `"8463528957154825"`
* `"dob"`: `"ad3420o23n434"`
* `"email"`: `"ko2390f32nf"`
**Data Privacy Vault (Center):**
The central block is labeled "Data Privacy Vault" and acts as an intermediary. The arrows indicate data flows *through* this vault.
**Destination 1: Support (Top-Right):**
The JSON data contains the following fields:
* `"full_name"`: `"John D***"` (partially redacted)
* `"ssn"`: `"*XXX-XX-3627*"` (partially redacted)
* `"dob"`: `"*REDACTED*"` (fully redacted)
* `"email"`: `"j***@gmail.com"` (partially redacted)
**Destination 2: Marketing (Bottom-Right):**
The JSON data contains the following fields:
* `"full_name"`: `"John Doe"`
* `"ssn"`: `"*REDACTED*"` (fully redacted)
* `"dob"`: `"XXXX-05-17"` (partially redacted)
* `"email"`: `"john.doe@gmail.com"`
### Key Observations
* Data is flowing from an unidentified source (represented by the hexadecimal string) and from a "Support" and "Marketing" department to the "Data Privacy Vault".
* The data shared with "Support" and "Marketing" is redacted, suggesting that the vault implements data masking or anonymization techniques.
* The source data contains a mix of alphanumeric strings and what appears to be a date of birth.
* The "Support" destination receives a partially redacted name and SSN, while the "dob" is fully redacted.
* The "Marketing" destination receives a fully redacted SSN and a partially redacted date of birth.
* The source data uses a non-standard date format.
### Interpretation
This diagram illustrates a data governance model where sensitive data is centralized in a "Data Privacy Vault". Access to this data is controlled, and different departments ("Support" and "Marketing") receive different levels of access based on their needs. The redaction of sensitive fields (SSN, DOB) suggests that the vault enforces data privacy regulations and minimizes the risk of data breaches. The use of a hexadecimal string as a source identifier could indicate data originating from a system or application with a unique ID. The diagram highlights the importance of access control and data masking in protecting sensitive information. The differing levels of redaction between the "Support" and "Marketing" destinations suggest a role-based access control system is in place. The diagram implies a need for data minimization, providing only the necessary information to each department.