## Sequence Diagram: Secure Summation Protocol
### Overview
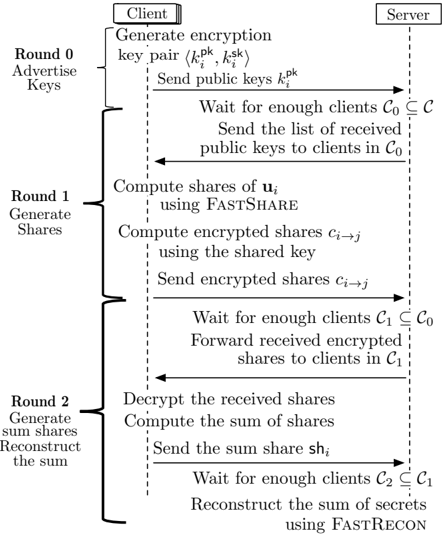
The image depicts a sequence diagram illustrating a secure summation protocol between a client and a server. The protocol is divided into three rounds: advertising keys, generating shares, and generating sum shares/reconstructing the sum. The diagram outlines the steps involved in each round, including key generation, share computation, encryption, decryption, and summation.
### Components/Axes
* **Entities:**
* Client (located at the top-left)
* Server (located at the top-right)
* **Rounds:**
* Round 0: Advertise Keys (left side)
* Round 1: Generate Shares (left side)
* Round 2: Generate sum shares/Reconstruct the sum (left side)
* **Messages:** Arrows indicate the flow of messages between the client and the server.
* **Processes:** Text descriptions detail the actions performed by each entity.
### Detailed Analysis or ### Content Details
**Round 0: Advertise Keys**
* **Client:**
* Generates an encryption key pair (k<sub>i</sub><sup>pk</sup>, k<sub>i</sub><sup>sk</sup>).
* Sends public keys k<sub>i</sub><sup>pk</sup> to the server.
* **Server:**
* Waits for enough clients C<sub>0</sub> ⊆ C.
* Sends the list of received public keys to clients in C<sub>0</sub>.
**Round 1: Generate Shares**
* **Client:**
* Computes shares of u<sub>i</sub> using FASTSHARE.
* Computes encrypted shares c<sub>i→j</sub> using the shared key.
* Sends encrypted shares c<sub>i→j</sub> to the server.
* **Server:**
* Waits for enough clients C<sub>1</sub> ⊆ C<sub>0</sub>.
* Forwards received encrypted shares to clients in C<sub>1</sub>.
**Round 2: Generate sum shares/Reconstruct the sum**
* **Client:**
* Decrypts the received shares.
* Computes the sum of shares.
* Sends the sum share sh<sub>i</sub> to the server.
* **Server:**
* Waits for enough clients C<sub>2</sub> ⊆ C<sub>1</sub>.
* Reconstructs the sum of secrets using FASTRECON.
### Key Observations
* The protocol involves three rounds of communication between the client and the server.
* Encryption and decryption are used to secure the shares.
* FASTSHARE and FASTRECON are used for share generation and reconstruction, respectively.
* The server waits for a sufficient number of clients in each round before proceeding.
* The sets of clients C<sub>0</sub>, C<sub>1</sub>, and C<sub>2</sub> are nested, with C<sub>2</sub> ⊆ C<sub>1</sub> ⊆ C<sub>0</sub> ⊆ C.
### Interpretation
The sequence diagram illustrates a secure summation protocol where a client distributes shares of a secret value to a server. The server aggregates these shares and reconstructs the sum without revealing the individual secret values. The use of encryption and specialized algorithms like FASTSHARE and FASTRECON ensures the privacy and security of the data during the process. The nested client sets (C<sub>0</sub>, C<sub>1</sub>, C<sub>2</sub>) suggest a progressive filtering or selection of clients involved in each round, potentially for efficiency or security reasons. The protocol is designed to allow the server to compute the sum of secret values held by multiple clients without learning the individual values themselves.